Why Turnkey for Enterprise Disaster Recovery?
Turnkey provides a secure foundation for disaster recovery. Our approach combines secure enclaves, end-to-end encryption, and programmable policies to ensure recovery material is protected at rest, in transit, and during use.Core principles
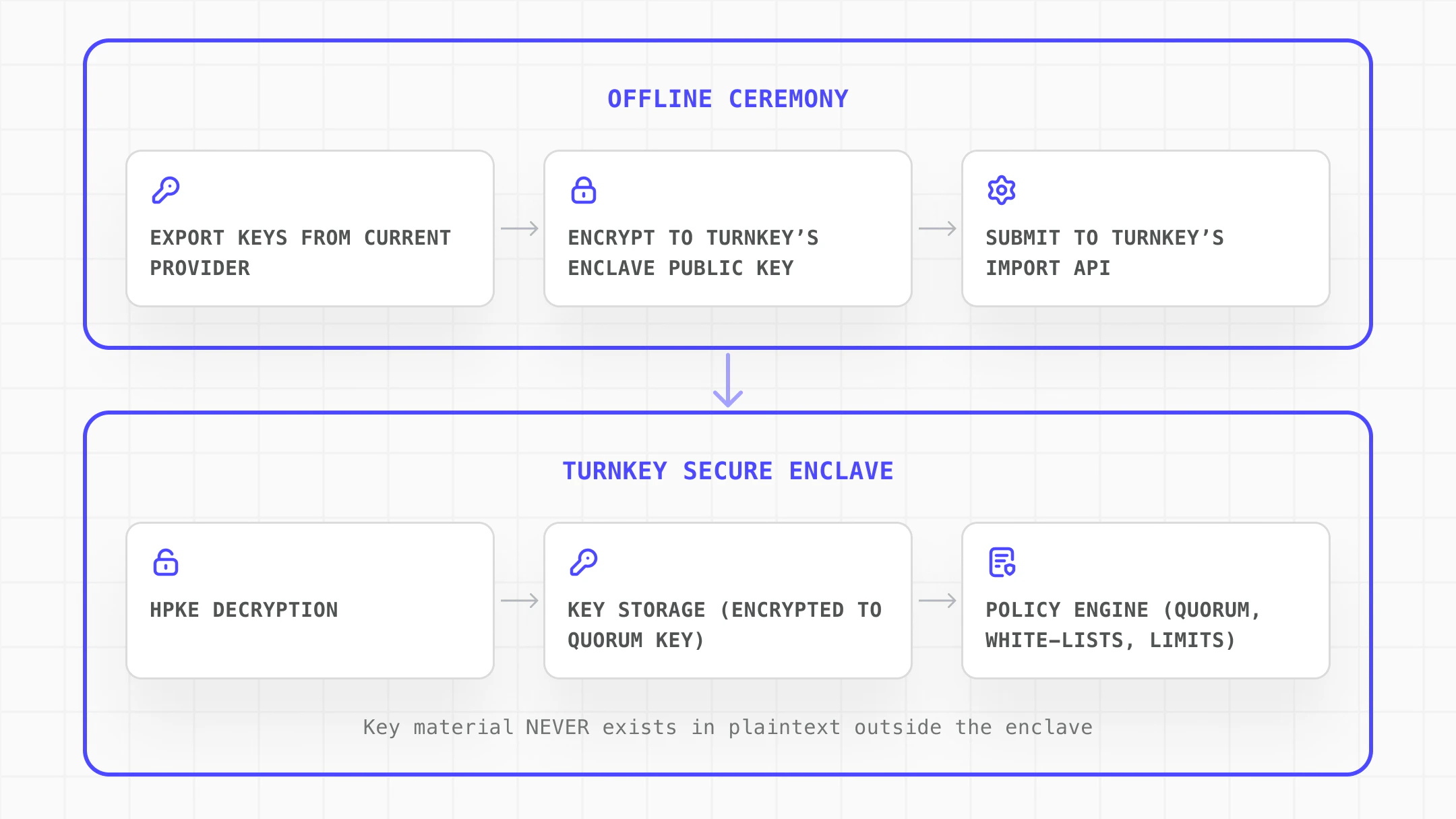
- End-to-end encryption: All key import material is encrypted directly to Turnkey’s secure enclave using HPKE (Hybrid Public Key Encryption). The plaintext never exists outside the enclave boundary.
- Cryptographic audit trail: Every recovery operation during transmission and import is cryptographically stamped, ensuring that recoveries can not be tampered with along the way.
- Policy-based guardrails: Turnkey’s policy engine restricts how wallets are accessed, like limiting fund movement to allowed addresses or requiring multiple approvals from your organization.
Direct Import Flow
How to Get Started on Enterprise Disaster Recovery with Turnkey
- Secure organization & policy setup: Create your Turnkey org, configure the root quorum, and define recovery policies.
- Set up the Turnkey SDK: Integrate React Wallet Kit or @turnkey/sdk-server into your application.
- Import wallets: Use handleImportWallet() to import wallet keys into Turnkey’s secure enclave.
Use Cases
| Need | Configuration |
|---|---|
| A key holder becomes unavailable or a hardware wallet fails, requiring immediate recovery of treasury assets. | Treasury recovery: Import wallet keys into Turnkey’s secure enclave with quorum-controlled access and policy-restricted fund sweeping. |
| Migrating from another key management provider with no plaintext exposure during transit. | Provider migration: Encrypt keys to Turnkey’s secure enclave on a hardened machine, import directly with full policy controls inherited immediately. |
| Operations need to continue even if a primary signer or infrastructure goes down. | Redundancy and failover: Import backup copies of critical wallet keys into Turnkey so a secondary signing path is always available. |
1. Secure Organization Setup and Recovery Policies
Create a Turnkey organization and establish the security foundation for recovery operations:- Create dedicated recovery users with specific, limited permissions
-
Configure the Root Quorum to require multiple approvers for
sensitive operations
- Require quorum approval for high-value operations to prevent any single person from unilaterally moving recovered funds. This ensures no single credential compromise can trigger unauthorized recovery. See Policy overview for setup guidance.
- Distribute authenticators (passkeys, YubiKeys) across geographic locations if possible
- Define policies that restrict what can be done with recovered wallets.
2. Set up the Turnkey SDK
Integrate Turnkey into your application to enable wallet import and recovery operations. The NodeJS server SDK is well oriented to handle the entire import flow, including encryption and secure transport.3. Import Wallets
Use importWallet() to import wallet keys into Turnkey’s secure enclave. In the last step the SDK encrypts the mnemonic or private key to Turnkey’s enclave public key using HPKE (Hybrid Public Key Encryption), and now transmits the encrypted bundle. The enclave decrypts and stores the key material. Plaintext key material never leaves the user’s device.The Result: Enterprise-grade Key Recovery
Turnkey transforms enterprise disaster recovery from a high-risk, manual operation into a secure, verifiable process. Import wallet keys directly into Turnkey’s secure enclave and gain immediate operational capability with full policy controls:- Cryptographic guarantees: Key material is protected by secure enclaves and end-to-end encryption
- Organizational controls: Quorum policies prevent unilateral action on sensitive operations
- Operational flexibility: Support for all major chains and key types through a unified interface
- Audit compliance: Every operation is logged with cryptographic signatures